We’ve made some significant improvements to SSH key management in the latest version of Transmit.
For a more consistent experience across all the Panic apps, Transmit 5 now natively supports generation, storage, and sync of SSH keys within the app, as well as using existing keys stored on your Mac.
For more information about key formats supported in Transmit 5, or how to use SSH keys, see our SSH Keys Guide.
How does SFTP Authentication work in Transmit 5?
TL;DR
- Username Preference Order
- Username defined in Transmit
- Username defined in
config
- Username defined in
- Shortname of current user on your Mac
- Password & Key Preference Order
- SSH Keys that have been added to the system SSH agent
- SSH Key defined in Transmit
- Passwords defined in Transmit
- SSH Key defined in
configor id files on disk
- SSH Key defined in
- Prompt for credentials during connection
Username Preference Order
When authenticating over SFTP Transmit will prefer usernames defined in the following order:
- Defined in Transmit
- A username saved with a Server or manually entered via Quick Connect
- As defined in
~/.ssh/config - Leave the username field in Transmit empty for usernames defined in your
config - The local user on your Mac
- If no username is defined Transmit will send the short name of the current user on your Mac by default.
Password & Key Preference Order
Transmit 5 uses passwords and keys in a specific order depending on where they exist on your Mac.
SSH Keys that have been added to the system SSH agent
The first authentication method attempted by Transmit are SSH keys that have been added to the system ssh-agent.
SSH key from Transmit’s Server settings
If you’re unfamiliar with how to add keys to the system agent, you can add keys directly to Transmit.
To associate an SSH key with a Server, import the key from a file on disk, or generate it right in Transmit.
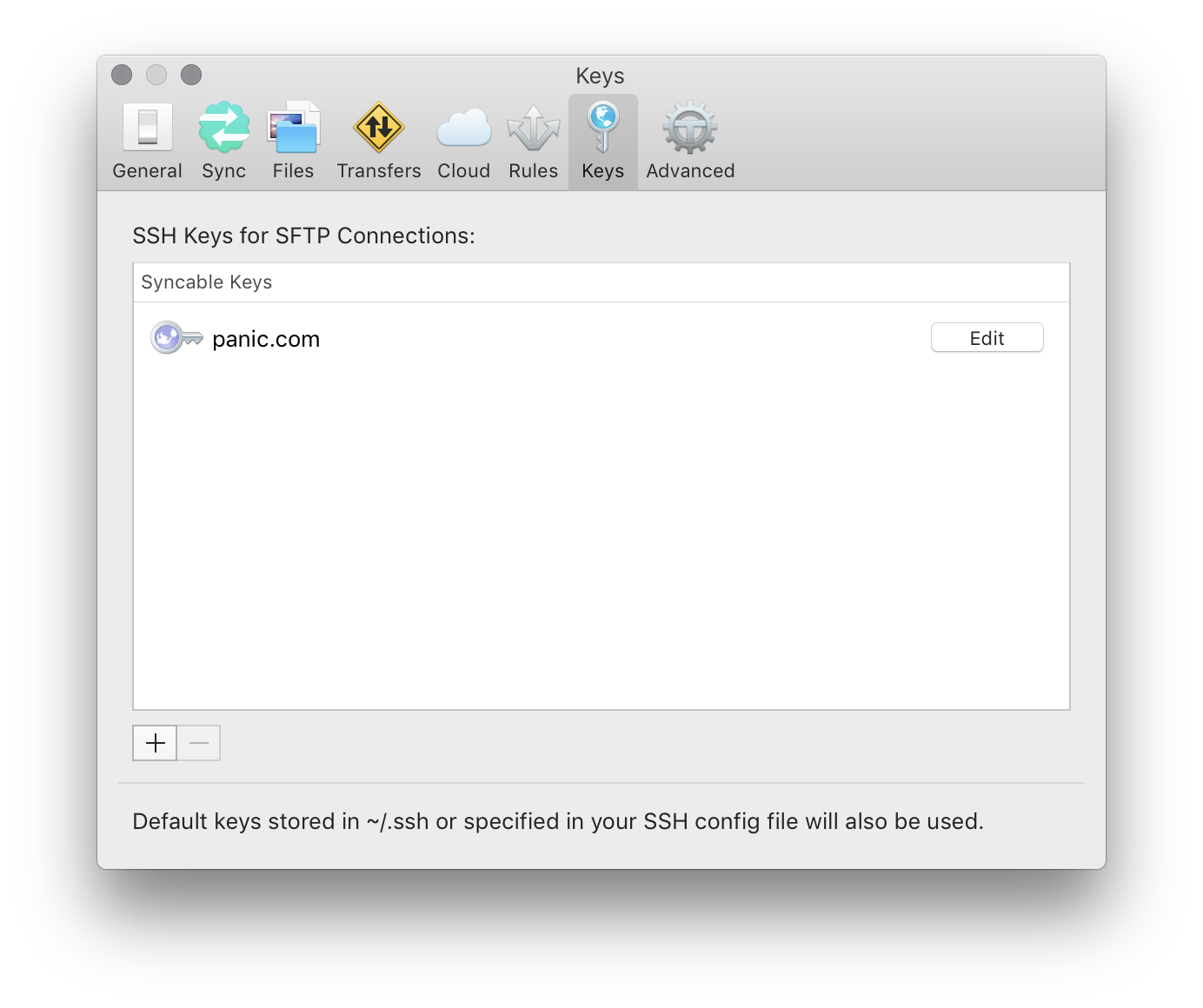
All key management is handled in the Keys tab of Transmit’s Settings menu. If you import an encrypted key, you will be prompted for the passphrase and it will be securely stored alongside the key in your system keychain.
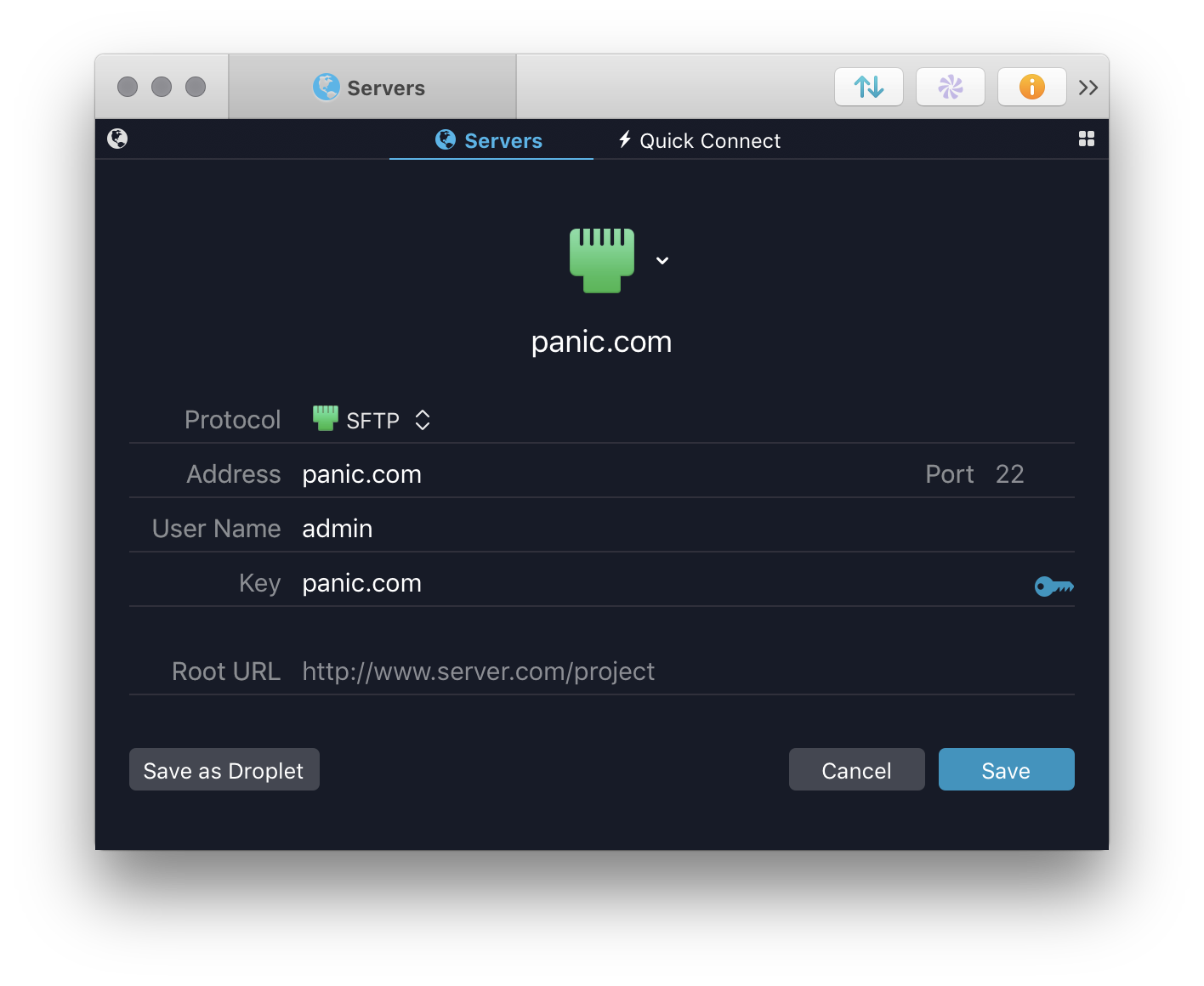
 After your key is imported, edit your Server and select the key you’d like to use for authentication.
If your key is encrypted and you chose not to store the passphrase, you will be prompted for it when you connect.
After your key is imported, edit your Server and select the key you’d like to use for authentication.
If your key is encrypted and you chose not to store the passphrase, you will be prompted for it when you connect.
Server password from Transmit Server settings
The next authentication method that Transmit will try is a password specified in the Server settings.
Please note: Passwords included in the Server settings will be used before SSH keys in the .ssh folder or config file
To use keys in your .ssh config file, or id keys in your ~/.ssh directory, do not save a password for the Server.
SSH key from SSH config file or id keys on disk
If the Server does not have a key or password associated with it, Transmit will attempt to use any keys specified for the server in your ssh config file, as well as any id keys (id_rsa, id_dsa, and id_ecdsa) in your ~/.ssh directory.
If these keys are encrypted and the passphrase is not stored in the keychain, Transmit will prompt you for the key’s passphrase when you connect to the server.
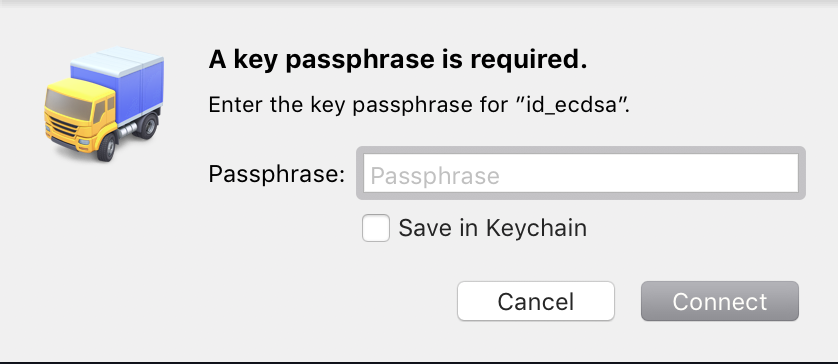
To skip authenticating with an encrypted key, leave the passphrase field blank and click Connect.
If you have existing keys on disk but do not want Transmit to attempt to use them when connecting, we recommend you specify a key or password with the Server.
Prompt for credentials when connecting
If you do not want to use an SSH key to connect, and also do not want to store your password in Transmit, Transmit will prompt for the server’s password at the time of connection.
I have two factor authentication turned on for my server, is that supported?
Yes! We support two factor authentication in conjunction with either key or password authentication.
The above order of operations still applies; a two factor code will be automatically requested during the process.
I have an SFTP favorite that connected in Transmit 4, but it doesn’t connect in Transmit 5. What’s going on?
In order to support the same authentication experience across all our Mac and iOS apps, Transmit 5 uses a different SSH library than Transmit 4.
Unfortunately, this means we have to temporarily drop support for a few features, specifically SFTP forwarding.
If you’re still having issues and do not use a SFTP proxy please contact our support team to have them assist with troubleshooting.